Many IT managers in Ireland assume that choosing a cloud provider with servers physically located in Ireland is enough to call their hosting "secure." That assumption is dangerously incomplete. Secure cloud hosting combines legal frameworks, technical safeguards, and operational disciplines that go far beyond geography. For Irish businesses running enterprise applications remotely, including ERP systems, accounting platforms, and databases, getting this wrong means failing audits, exposing sensitive data, and breaching GDPR obligations. This guide maps every layer of the puzzle.
Table of Contents
- What is secure cloud hosting?
- Key pillars of secure cloud hosting for Irish businesses
- Comparing secure VPS cloud hosting: Security, scalability, and compliance
- Implementing secure cloud hosting: Best practices and common pitfalls
- The overlooked reality: Why secure cloud hosting is never 'set-and-forget'
- Expert secure cloud hosting solutions for Irish enterprises
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Security is multi-layered | Where your data is hosted is just one piece; processes, legal compliance, and ongoing management are just as essential. |
| Irish regulations demand more | Compliance in Ireland and Europe involves specific legal mechanisms for all cloud setups handling enterprise data. |
| VPS stands out for compliance | VPS cloud hosting balances strong security, flexibility, and regulatory alignment for most Irish business cases. |
| Ongoing monitoring is critical | Treat secure hosting as an evolving process, with regular checks, audits, and improvements to stay compliant. |
What is secure cloud hosting?
Secure cloud hosting means running workloads on remote infrastructure where every layer, physical, network, application, and operational, is actively protected against unauthorized access, data loss, and service disruption. It is not a single feature. It is a framework.
For Irish businesses managing remote teams or running applications like Sage, Xero, or SQL-based ERP tools, the stakes are high. A misconfigured firewall, an unpatched operating system, or a missing backup can turn a routine hosting setup into a costly incident. Understanding the layers gives your team a clearer target.
The core components of secure cloud hosting include:
- Physical security: Data center access controls, CCTV, biometric locks, and hardware redundancy.
- Network security: Firewalls, DDoS protection, encrypted VPN tunnels, and intrusion detection systems.
- Application security: Patching schedules, role-based access controls (RBAC), and secure remote desktop configurations.
- Operational security: Backup policies, incident response plans, and audit logging.
- Legal and compliance controls: GDPR-aligned data processing agreements, data classification, and transfer mechanisms.
Virtual Private Servers, or VPS, emerged as a solution that fits squarely in this framework. Unlike shared hosting, a VPS gives your organization dedicated, isolated resources on a shared physical machine. You get root-level control, a defined security boundary, and predictable performance. You can learn more about why secure business growth with VPS depends on choosing the right architecture from the start.
This model becomes essential when your team accesses applications remotely. Remote Desktop Services running on a Windows VPS, for example, create an edge between user devices and the core server. That edge introduces risk. A server cloud management overview shows why managing access points across this architecture requires deliberate planning.
Pro Tip: Your monitoring strategy cannot stop at the server boundary. As edge-monitoring best practices confirm, remote-access operations require coverage across edge-to-cloud traffic, standardized log structures for ingestion, and incident response plans that account for edge-specific constraints like latency and device reachability.
"Secure cloud hosting is not a destination. It is a posture that your team earns and maintains every single day through policy, technology, and vigilance."
Key pillars of secure cloud hosting for Irish businesses
Having set the groundwork, let's explore what makes cloud hosting truly secure for an Irish enterprise. The pillars are technical, organizational, and legal. All three must work together. Weakness in any one pillar creates a gap that attackers or auditors will find.
Here are the essential pillars in priority order:
-
Data sovereignty and residency: Know where your data lives and under which legal jurisdiction. Irish businesses operating under GDPR must understand that cloud computing compliance goes far beyond geography. Where data is hosted is only part of the story. Secure procurement and legal compliance involve data protection transfer mechanisms and EU cloud governance expectations that apply regardless of server location.
-
Procurement and vendor due diligence: Before signing any hosting contract, verify that the provider offers a Data Processing Agreement (DPA) that meets GDPR Article 28 standards. Check their sub-processor list. Confirm their breach notification timelines meet the 72-hour GDPR window. Skipping this step at procurement creates legal exposure that no technical control can fully patch later.
-
User access management: Implement least-privilege access across every system. For Windows VPS environments running RDS, this means assigning users only the permissions they need for their specific applications. Multi-factor authentication (MFA) is non-negotiable. Without it, a stolen credential becomes a full breach.
-
Legal transfer mechanisms: If any data crosses EU borders, even temporarily, your organization needs Standard Contractual Clauses (SCCs) in place. The EU Data Act and evolving guidance from the Data Protection Commission of Ireland mean Transfer Impact Assessments (TIAs) are increasingly expected. Treat these as living documents, not one-time checkboxes.
-
Technical controls: Encryption, backup, and monitoring: Data must be encrypted in transit and at rest. Automated backups with tested restore procedures protect against ransomware and hardware failure. Continuous monitoring with alerting closes the loop. A secure, scalable hosting in Ireland setup covers these controls from day one rather than bolting them on after deployment.
-
Incident response planning: Your plan must account for the reality of remote and edge access. A breach that starts at a remote desktop session or a VPN endpoint needs a different containment response than one originating in the data center itself.
Pro Tip: Before going live with any new hosting environment, run a tabletop exercise that simulates a breach from a remote access point. You will quickly discover gaps in your secure VPS setup guide that no checklist would have caught.
A notable statistic worth keeping in mind: the average cost of a data breach in Europe now exceeds €4 million per incident. For SMEs, that figure can be existential. The pillars above are not optional extras. They are the minimum baseline.

Comparing secure VPS cloud hosting: Security, scalability, and compliance
Now, it's essential to see how different cloud hosting approaches stack up, and why VPS dominates for compliance-critical workloads in Ireland.
| Feature | Shared hosting | VPS cloud hosting | Dedicated server |
|---|---|---|---|
| Resource isolation | None | Full | Full |
| Security boundary | Shared | Dedicated per instance | Dedicated |
| Scalability | Limited | High, on demand | Low, hardware-bound |
| GDPR auditability | Difficult | Strong | Strong |
| RDS/Windows Server support | Rare | Standard | Standard |
| Cost efficiency | High | Medium | Low |
| Compliance fit | Poor | Excellent | Excellent |
| Deployment speed | Fast | Very fast (minutes) | Slow (days/weeks) |
The table makes the tradeoffs clear. Shared hosting may cost less, but the absence of resource isolation makes it nearly impossible to demonstrate compliance with GDPR's data minimization and access control principles during an audit. Dedicated servers offer strong isolation but sacrifice the flexibility and speed that modern Irish businesses need when scaling up for a busy quarter or onboarding a new team.
VPS sits in the optimal position for most enterprise workloads. It delivers the isolation and auditability of dedicated hardware at a fraction of the cost, with the elasticity of cloud. The key is selecting a VPS provider with pre-configured Windows Server environments and RDS licensing included, so your team does not spend weeks on initial configuration before they can work.
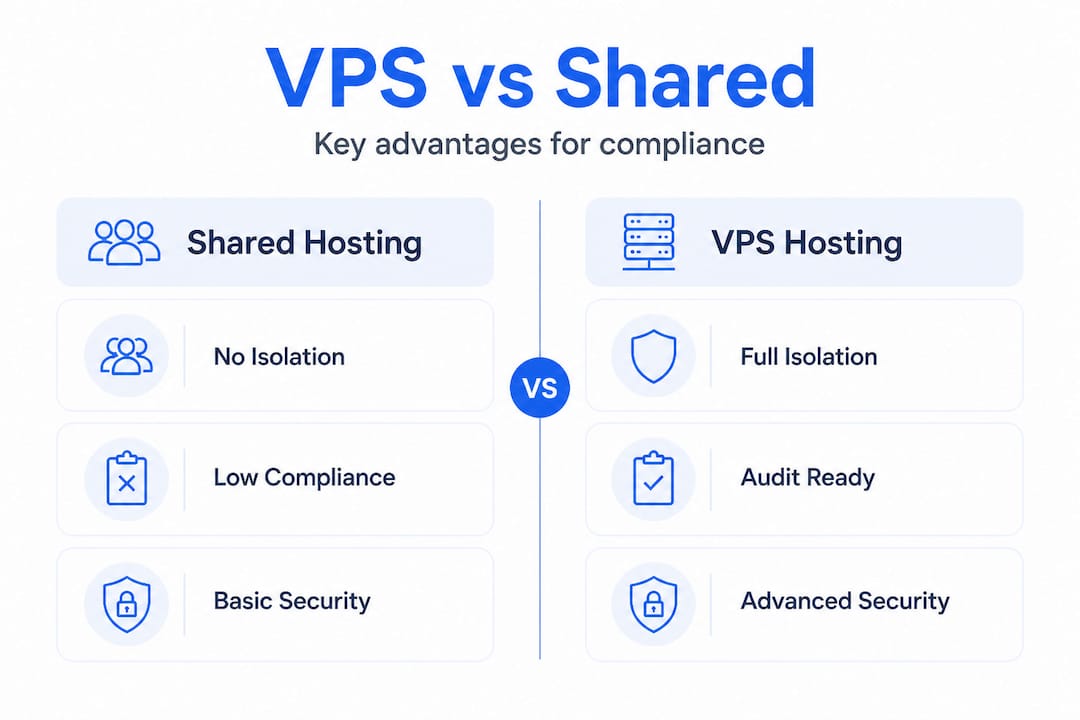
A useful review of hosting options comparison confirms that VPS consistently outperforms shared environments for businesses with compliance requirements. For Irish businesses specifically, the Windows VPS security checklist gives you a practical framework for verifying your configuration before go-live.
For remote teams, VPS with RDS creates a centralized application environment that workers access from any device. The server stays inside the security boundary. The data never touches the employee's local machine. This architecture is a strong defense against endpoint-based data leaks. More guidance for distributed teams is available in VPS for remote work performance guidance for IT leaders.
One critical insight that separates high-performing IT teams from the rest: the best VPS security posture is not a one-time configuration. As FedRAMP's monitoring guidance explains, benchmark-driven security works best when treated as an ongoing control loop: detect misconfiguration drift, prioritize remediation by severity, and keep auditable evidence for auditors rather than relying on "configure once and forget." Irish organizations should adopt this mindset from day one.
Implementing secure cloud hosting: Best practices and common pitfalls
With the comparison in mind, let's turn theory into a step-by-step path for secure implementation. The sequence below applies whether you are migrating an existing workload or building a new environment from scratch.
Step-by-step secure deployment sequence:
- Plan: Define your data classification policy. Identify which data types will live on the VPS, who needs access, and which compliance frameworks apply, primarily GDPR, but also any sector-specific rules like those for healthcare or finance.
- Configure: Deploy your secure VPS setup with hardened Windows Server settings. Disable unused services, set up firewall rules, enable MFA for all RDS users, and configure VPN access.
- Test: Run penetration testing and vulnerability scans before going live. Test backup restoration. Verify that monitoring alerts fire correctly. Confirm that your logging captures the events your DPA and incident response plan require.
- Monitor: Activate continuous monitoring across the full edge-to-cloud path. Standardize log formats so your SIEM or monitoring tool can ingest and correlate events from VPN endpoints, RDS sessions, and the server itself. As edge-monitoring best practices note, incident response plans must reflect edge-specific constraints including latency and device reachability.
- Document: Maintain records of every configuration change, access grant, and security review. Auditors expect evidence, not promises.
Common pitfalls and how to fix them:
| Pitfall | Why it happens | Fix |
|---|---|---|
| No MFA on RDS | Seen as extra friction | Enforce via Group Policy or Azure AD |
| Infrequent backups | Default settings not reviewed | Set daily automated backups with offsite copy |
| No patch schedule | "It's working, don't touch it" | Set monthly patching windows with test procedure |
| Shared admin credentials | Team convenience | Individual admin accounts with RBAC |
| No incident response plan | Assumed to be IT's problem | Document, test, and include legal/compliance team |
| Missing DPA with provider | Procurement oversight | Require DPA before signing any contract |
Pro Tip: Every time your team makes a significant change to your VPS environment, including adding a user, updating firewall rules, or changing backup schedules, treat it as a compliance event. Loop in both IT and your data protection officer or compliance lead. This discipline costs minutes but saves hours during audits.
The overlooked reality: Why secure cloud hosting is never 'set-and-forget'
Before wrapping up, it is vital to challenge the most damaging misconception in secure cloud hosting for Irish businesses. Most IT teams treat cloud security as a project with a finish line. They configure the firewall, deploy the VPS, set up backups, and move on. Months later, an audit reveals configuration drift, expired certificates, or access accounts for employees who left the company a year ago.
This is not a rare failure. It is the norm. And the reason is understandable. IT teams are stretched thin, and security maintenance lacks the visibility of a new deployment or a critical outage. But the consequences are severe.
We have seen this pattern repeatedly. A business invests in strong initial configuration but skips the ongoing review cycle. When an auditor or, worse, a breach forces a review, the gap between the intended security posture and the actual state is jarring. FedRAMP's security guidance frames this precisely: security posture works best as an ongoing control loop where you detect misconfiguration drift, prioritize remediation by severity, and keep auditable evidence continuously, not just at audit time.
For Irish businesses, GDPR adds a legal dimension to this discipline. The Data Protection Commission expects organizations to demonstrate ongoing accountability, not just initial compliance. "We set it up correctly two years ago" is not a defense if your current state does not reflect that.
The practical fix is straightforward even if it requires organizational commitment. Schedule quarterly security reviews that cover access controls, patch levels, backup test results, and log retention. Assign ownership. If nobody is accountable for the review, it will not happen. Connect these reviews to your incident response plan and your growth through secure VPS hosting roadmap so security improvement aligns with business growth rather than trailing behind it.
Remote access makes this discipline even more critical. Every new remote user, every new device, and every new application creates potential drift. Treat your VPS security posture as a living document, updated with every change and reviewed on a fixed schedule.
Expert secure cloud hosting solutions for Irish enterprises
With rigorous standards now clear, discover how specialized Irish VPS solutions deliver true security and regulatory peace of mind. At Netcloud24, we have built our hosting environment specifically for Irish businesses that need more than a generic cloud server.
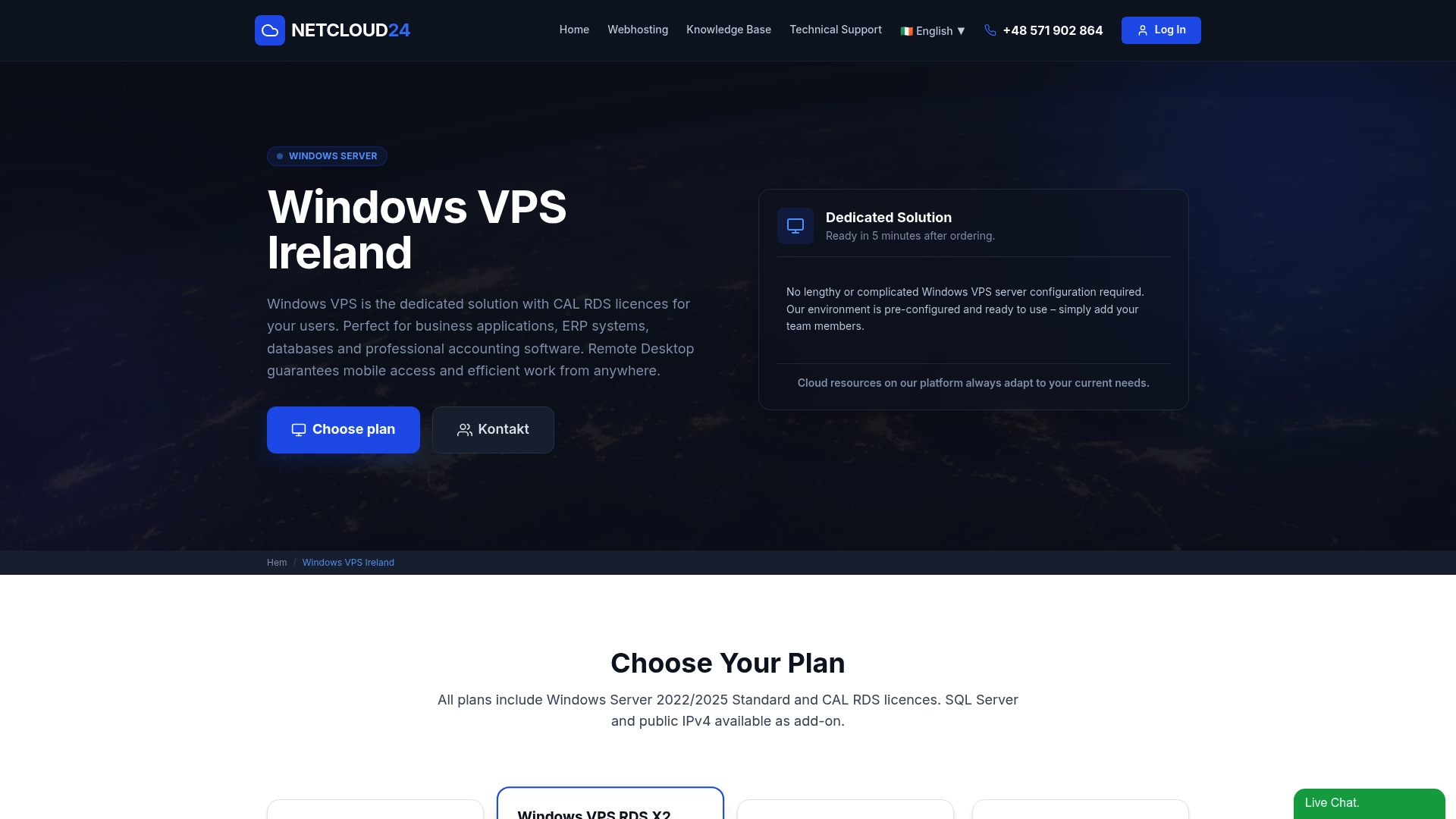
Every Microsoft SQL Windows VPS Server we provide comes pre-configured with Windows Server and RDS licensing, NVMe enterprise storage, built-in firewall and VPN access, automatic backups, and GDPR-aligned data processing agreements. Your environment is live within five minutes, not five weeks. Whether your team runs Sage, Xero, SQL databases, or custom ERP applications, our platform is designed to support secure multi-user remote access from day one without requiring your IT team to configure security from scratch.
Frequently asked questions
What is the difference between secure VPS and regular cloud hosting?
Secure VPS provides fully isolated resources and dedicated security controls that make compliance audits straightforward, while regular shared cloud hosting pools resources across customers and lacks the clear security boundaries that GDPR-sensitive workloads require. VPS security advantages are especially significant for businesses managing confidential financial or personal data.
Do Irish regulations require data to stay within the country?
No mandatory data residency requirement forces data to remain in Ireland, but Irish and EU rules impose strict legal obligations on cross-border transfers, including Standard Contractual Clauses and Transfer Impact Assessments. As the Cloud Computing Advice Note 2025 makes clear, legal compliance involves far more than server location.
Is edge monitoring necessary for remote access setups?
Yes, absolutely. Remote and edge access introduce unique risks including session latency, device vulnerabilities, and limited visibility into connection endpoints. Edge-to-cloud monitoring coverage and edge-specific incident response plans are required for any mature security posture.
How often should security configurations be reviewed?
Security configurations should be reviewed on a continuous or at minimum quarterly basis, with changes documented after every significant update. Ongoing security control loops that detect misconfiguration drift and maintain auditable evidence are far more effective than annual point-in-time reviews.
Recommended
- Pre-Configured VPS: Secure, Scalable Hosting for Irish Enterprises
- Secure VPS setup for enterprise access in Ireland
- Microsoft SQL Windows VPS Server, IIS & ASP.NET VPS Hosting | Remote Access & RDS Ready
- VPS for remote work: A performance guide for IT leaders
- How to Secure Your Data: Essential Steps for Protection – buy2fix
- WordPress Hosting & Maintenance - Media House Agency
